CyberVertrauen is not a message. It’s a response capability.
One recent case went from first customer contact to an operational response rollout in just 14 hours (!) – a reminder that in cybersecurity, trust is proven by speed.
This article was triggered by a real event that unfolded exactly this way. Watching the timeline of that incident made something very clear to me: in cybersecurity, proximity is not a secondary factor. It can determine how quickly trust turns into action.
What stood out was not only the technical response. It was how quickly people aligned, how directly communication worked, and how little friction there was between those involved. The timeline showed that proximity matters – not only in location, but operationally: in responsiveness, in coordination, and in the ability to create clarity when pressure is highest.
CyberVertrauen does not live in a claim. It becomes visible when a promise has to hold under pressure.
In my last (and first) article here on substack, I wrote that our rebrand is not a design exercise, but a decision about trust. My point was that clarity, positioning, and simplicity matter more in a market where AI is accelerating commoditization and making many parts of technology easier to build and easier to compare.
But trust does not earn its meaning in a brand book. It earns its meaning in the moment when words have to become action.
That is especially true in cybersecurity. Customers do not buy technology alone. They buy the confidence that, when the situation becomes critical, someone will take ownership, move quickly, and turn uncertainty into a workable path forward.
That is why trust in our industry is not a soft factor. It is what makes capability credible.
Trust is proven operationally
You can see that most clearly when a SOC or managed security service has to be rolled out directly after an incident. In those moments, architecture, features, and documentation matter far less than many people think. The real question is whether different teams can become one functioning response system fast.
A recent case made that very clear to me. After an acute security incident, a customer needed support immediately (24.03.26 – 11:42pm). What stood out was not one spectacular move. What stood out was that the chain held: no unnecessary loops, no friction, no debate about ownership. People aligned, decisions moved, and capability reached the customer quickly – the rollout started (25.03.26 – 14:03pm). 14 hours and 21 minutes from initial contact to the start of the rollout.
That is the real test. In moments like these, trust either becomes visible or it doesn’t.
Why speed matters so much after a ransomware attack
After a ransomware attack, the real danger is often not over. In many cases, the risk intensifies almost immediately. Cybereason reports that 80% of organizations that paid a ransom were hit again, and 68% said the second attack came in less than a month.1
That is why fast onboarding after an incident is not an operational detail. It is part of the actual security promise.
When onboarding starts too late, companies lose exactly the window in which trust and operational capability matter most. The critical phase starts right after the first incident, not weeks later.
But speed after an incident is not only about restoring operations. It is about knowing whether the environment is actually clean.
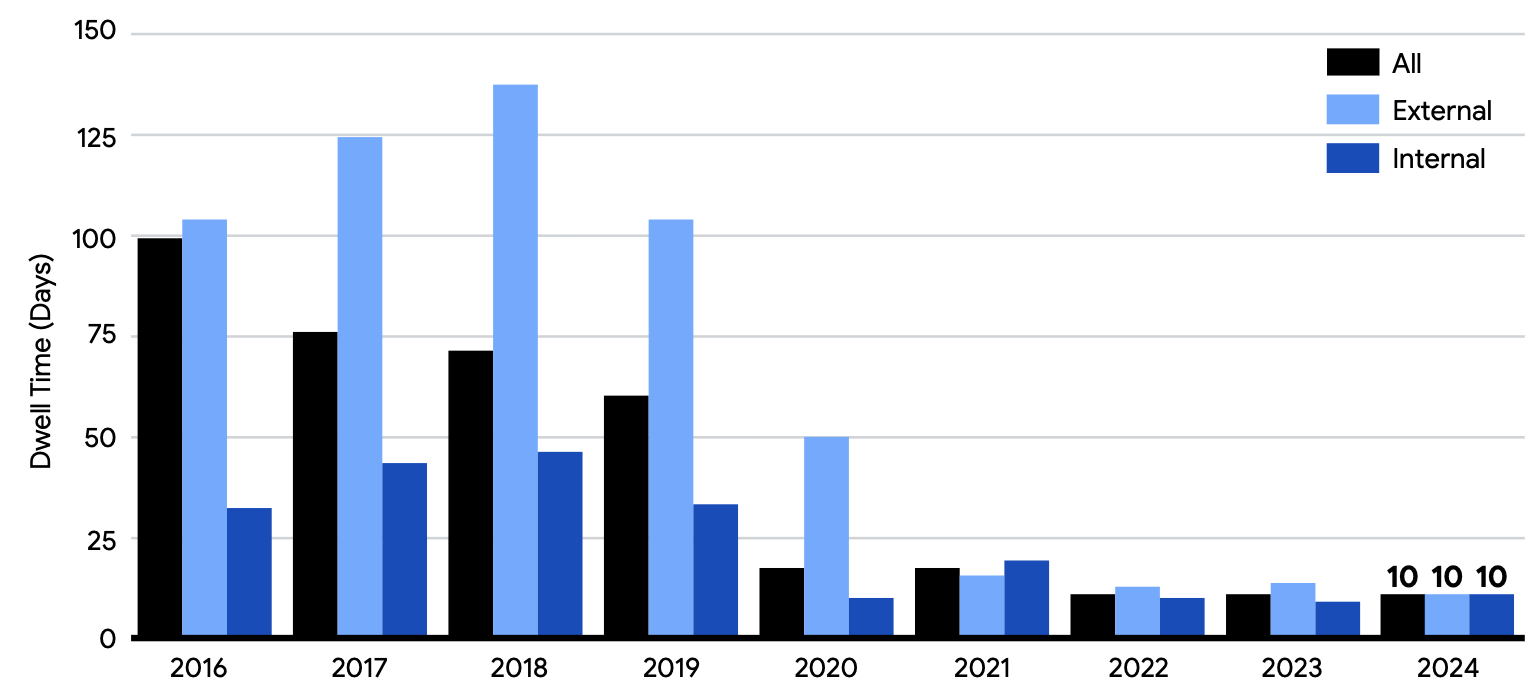
That is where continuous monitoring becomes decisive. Mandiant reported a global median dwell time of 10 days for 2024.2 In cases where discovery came through external notification, dwell time rose to 26 days. Those numbers make one thing very clear: without immediate visibility, attackers can remain active long after the first response appears complete.
That is exactly why there must be no monitoring gap after technical remediation. Persistence mechanisms, reinfection, or remaining access paths may otherwise stay invisible until damage occurs again. A SOC rolled out immediately after the incident closes that gap. It validates whether remediation actually worked, detects relapse early, and reduces both the damage window and the response time if suspicious activity returns.
Partners are more than a route to market
What continues to stand out to me in these situations is the role of the partner model. Partnerships are often discussed in go-to-market terms: reach, scale, customer proximity. All of that matters. But in security, it is only part of the story.
In an actual incident, partners are not just a sales channel. They are part of the trust chain.
When vendor, partner, and service teams work in sync, the customer gets what matters most in a critical situation: orientation, speed, and the sense that they are not facing the problem alone. When that coordination breaks down, valuable time is lost – and with it, often trust as well.
That is why the strength of a functioning partner model is not just market coverage. It is the ability to become operational together under pressure.
Simplicity is not only a brand principle
One of the core ideas I took from the first article was that simplicity is not cosmetic. It is strategic. And that does not apply only to brand leadership.
It applies operationally as well.
In critical situations, customers do not need more complexity. They need clear next steps, clear responsibilities, and clear communication. They are not looking for a system that performs depth. They are looking for a setup that creates orientation quickly and becomes effective fast.
That is exactly why simplicity matters so much in the rollout of a SOC or managed security service. It reduces friction, speeds up decisions, and makes collaboration more resilient. And it directly strengthens the very thing the industry talks about so often, but too rarely turns into lived reality: trust.
Why cases like this matter
Not every important case is a large one. But some cases reveal with unusual precision what really matters.
They show whether people, processes, and responsibilities are aligned well enough to turn a critical situation into a structured path forward. They show whether partners, vendors, and service teams are merely working alongside each other or truly with each other. And they show whether the customer experiences what the brand promises: clarity, reliability, and operational readiness – what we call #CyberVertrauen.
That is the point where positioning becomes real.
That is the point where CyberVertrauen stops being a communications concept and becomes something tangible.
Conclusion
The more complex technology becomes, the more valuable the ability to make that complexity manageable for customers becomes. That is the connection, for me, between our rebrand and the operational reality of a SOC or managed security rollout.
CyberVertrauen is not built in theory. It is built when people take ownership at the right moment, when partners and vendors work without friction, and when technical capability turns quickly into real help.
In cybersecurity, what matters in the end is not only what a provider can do.
What matters is how clearly, how quickly, and how reliably that capability reaches the customer.
CyberVertrauen is not what a provider says before an incident. It is what the customer experiences when everything suddenly depends on execution.
https://www.cybereason.com/blog/ransomware-attacks-by-the-numbers-and-how-to-defend-against-them
https://services.google.com/fh/files/misc/m-trends-2025-en.pdf
